苹果Mac电脑再曝密码绕过漏洞
|
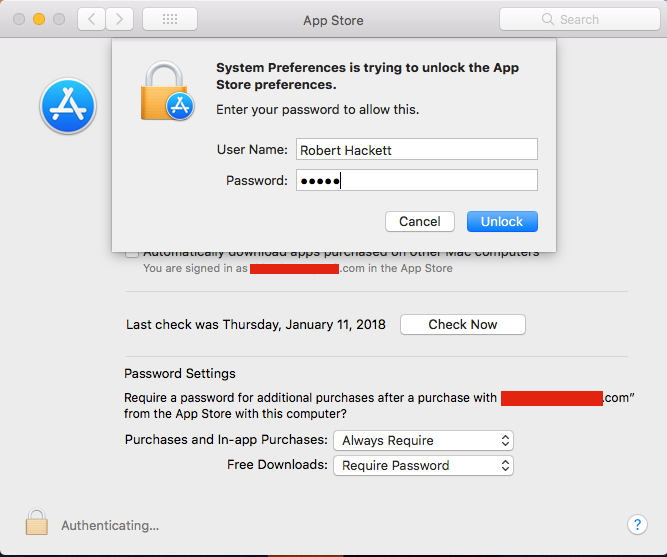
运行苹果最新版High Sierra操作系统的苹果Mac计算机曝出漏洞,可以让任何人输入任意密码来解锁并修改应用商店的偏好设置。 苹果在去年11月末也曝出了漏洞:只需输入用户名“root”,并进入Mac电脑系统偏好菜单“用户与群组”栏目,便可获得苹果Mac电脑更高的管理员权限。因此,这一漏洞与其相比可谓是小巫见大巫。在打补丁之后,11月底发现的这个安全漏洞可以让任何人对电脑进行物理访问,并查看任何文件或修改和重设其他用户的任何密码。 新漏洞由IT系统管理员艾瑞克·霍尔塔曼发现并上传至漏洞报告网站Open Radar。不管怎么样,这个漏洞也引起了人们的不安。虽然它的严重性远不及上一个漏洞,但也让人们开始对苹果的安全设计产生了质疑,毕竟这是近几个月来发现的第二个登录小漏洞。 致力于报道苹果的博客MacRumors首先公布了霍尔塔曼在上周二发布的贴文。 利用这一漏洞的步骤如下: 1. 打开“系统偏好”。 2. 选择“应用商店” 。 3. 点击挂锁标志来“解锁”(如果处于“未解锁”状态)。 4. 点击挂锁标志解锁。 5.输入你的用户名和任意密码。 屏幕上将显示以下提示信息: |
Apple Mac computers running the latest version of Apple’s High Sierra operating system have a flaw that lets just about anyone unlock and edit a person’s App Store preferences with any password. The vulnerability isn’t nearly as bad as one discovered in late November that allowed anyone to obtain higher, administrative privileges on Apple Mac computers merely by entering the username “root” while logging into the “User & Groups” section of a Mac computer’s System Preferences menu. That earlier security hole, since patched, enabled anyone with physical access to a machine to view any files or change and reset any passwords for other users. The new flaw, uncovered by Eric Holtam, an IT systems administrator, and posted to Open Radar, a bug-reporting website, is troubling nonetheless. The finding, though far, far less serious than the past blunder, raises concerns about Apple’s (AAPL, +0.57%)security design, given that this is the second trivial login bug to come to light in recent months. MacRumors, a blog devoted to Apple coverage, first spotted Holtam’s post on last Tuesday. Here are the steps to follow to exploit the hole: 1.Open “System Preferences”. 2.Select “App Store” . 3.Click the padlock icon to “lock” it (if it is “unlocked”). 4.Click the padlock icon to “unlock” it. 5.Enter your user name and any password. Here’s what the screen should display: |
|
在解锁应用商店偏好之后,人们可以更改某些密码设置,例如在批准应用相关购买时系统要求用户输入密码的频率。即便如此,攻击者也无法随心所欲地去进行修改,因为只有“始终要求输入”或“15分钟后要求输入”这两个选项。 严重警告:任何希望利用这一验证绕过漏洞的人必须以管理员的身份登录电脑。当《财富》杂志在2015年Macbook Air笔记本上使用非管理员账户测试这一漏洞时,所有的尝试均以失败告终。 苹果似乎在即将到来的mac OS High Sierra升级(10.3.3)的早期版本测试这一漏洞的补丁。这一问题很有可能在未来的软件升级中得到解决。 苹果并没有对评论要求做出立即回应。(财富中文网) 译者:冯丰 审稿:夏林
|
After unlocking App Store preferences, a person can tweak certain password settings, such as the frequency with which a system asks for a user’s password when approving app-related purchases. Even so, attackers cannot go on prolonged spending sprees: the two options are “Always require” or “Require after 15 minutes.” One big caveat: anyone looking to take advantage of this authentication sidestep has to be logged in as an administrator. When Fortune tested the approach on a 2015 Macbook Air using a non-administrator account, all attempts failed. Apple appears to be testing a patch for the bug in an early version of a coming macOS High Sierra upgrade (10.3.3). It’s likely the issue will be resolved in a future software update. Apple did not immediately reply to a request for comment. |